Public API
To automate your Escape scans, you can use the Escape REST API.
API Base URL & OpenAPI Documentation (V3)¶
V3 API is in beta
The V3 API is in beta and is subject to change.
The Escape REST public API documentation is available at https://public.escape.tech/v3/.
The OpenAPI specification is also downloadable from https://public.escape.tech/v3/openapi.json.
Breaking payload migration notice¶
Upcoming input format changes
The following request fields are migrating from JSON-encoded strings to JSON objects:
POST /v3/profiles/*->configuration(preferred, object)POST /v3/assets/schema->authentication(preferred, object)POST /v3/scans->configurationOverride
Compatibility note for POST /v3/profiles/*: both object configuration and legacy JSON-string configuration are accepted for now.
Compatibility note for POST /v3/assets/schema: both authentication and legacy authenticationStr are accepted for now.
Please migrate to object payloads and treat legacy string fields as deprecated.
Legacy string fields will be removed in a future API version.
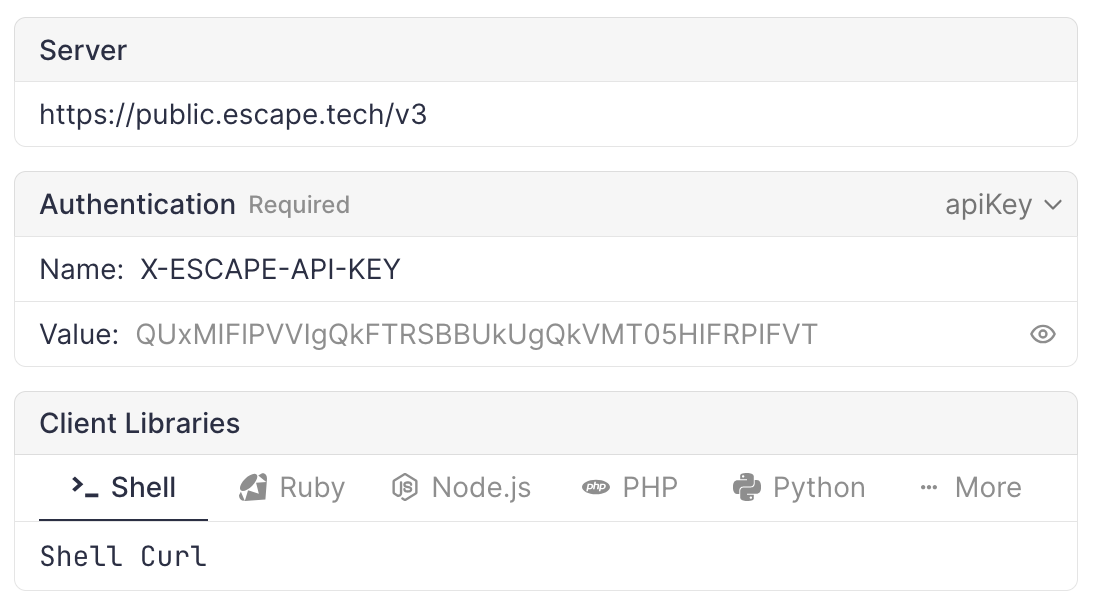
Authentication using API Key¶
To authenticate your requests, you need to pass your API key as headers.
You can find your API key in your Escape settings.
Now you can add the following header to your requests:
In the web UI, you can set the API key in the top section of the page, it will be used for all your requests.
Basic Example¶
export API_KEY=<YOUR API KEY>
# List profiles
curl -H "X-ESCAPE-API-KEY: $API_KEY" https://public.escape.tech/v3/profiles
Retrieving API coverage in CI/CD¶
You can use the Public API to read aggregate coverage for a finished scan and per-endpoint coverage for automation (for example, failing a pipeline when coverage is below a threshold or when critical operations stay UNAUTHORIZED).
-
Aggregate ratio — After the scan has finished,
GET /v3/scans/{scanId}andGET /v3/scansreturn a nullablecoveragefield (0–1) when Escape has computed scan-level coverage for that run. Profile detail (GET /v3/profiles/{profileId}) still exposes the application’s currentcoverageand embeds the last scans as today. -
Endpoint-level detail —
GET /v3/scans/{scanId}/targetsreturns paginated targets. For REST and GraphQL API targets, the nestedapiRouteandgraphqlResolverobjects includecoverage, optionalcoverageByUser, andmeanDuration. Use query parameterscursor,size, and optionallytypes(for exampleAPI_ROUTEorGRAPHQL_RESOLVER) to page and filter.
The meaning of each coverage status (OK, UNAUTHORIZED, BLOCKLISTED, and so on) is documented in Analyze Coverage. The full request and response shapes are in the OpenAPI specification and interactive docs at public.escape.tech/v3.
Listing scans with problems¶
GET /v3/scans/problems returns scans together with the validation problems surfaced by the scanner during execution (broken authentication, unreachable target, invalid schema, etc.). It is the scan-indexed counterpart of GET /v3/profiles/problems, which groups problems by profile.
The response is a paginated list of scans, each decorated with a problems array. You can filter by assetIds, profileIds, projectIds, status, kinds, initiator, after, before, and ignored. Pagination uses cursor and size. See the OpenAPI specification for the full request and response schemas.
The equivalent CLI command is escape-cli scans problems.
Creating AI Pentesting profiles (Beta)¶
Beta
The AI Pentesting profile endpoint is in beta and may change.
You can create AI Pentesting profiles via the API, in addition to the existing DAST profile types. A single endpoint creates a profile for any supported asset; the asset’s type determines the scan surface (REST, GraphQL, or web application).
| Endpoint | Description |
|---|---|
POST /v3/profiles/ai-pentest |
Create an AI Pentesting profile (all supported targets) |
The request body is the same as for DAST profiles (assetId, name, configuration, mode, etc.). See Scan mode for the mode parameter.
curl -X POST https://public.escape.tech/v3/profiles/ai-pentest \
-H "X-ESCAPE-API-KEY: $API_KEY" \
-H "Content-Type: application/json" \
-d '{
"assetId": "<ASSET_ID>",
"name": "AI Pentest - Production WebApp",
"mode": "read_only"
}'
The full request and response schemas are available in the OpenAPI specification.
Enforcing a rate limit across many profiles¶
PUT /v3/profiles/{profileId}/configuration accepts the full scanner configuration, so network.requests_per_second (range 1–1000, default 100) can be set programmatically for any profile. Combined with GET /v3/profiles (paginated, filterable by tagIds, search, domains), this lets you roll out a uniform rate limit across every profile that scans a given environment — for example every profile bound to a Private Location that targets monitoring-sensitive internal infrastructure.
The Rate Limiting Private Location Scans cookbook walks through a minimal script, a scheduled re-enforcement workflow, and the equivalent one-shot MCP tool.
PUT replaces the full configuration body
Always read the existing configuration with GET /v3/profiles/{profileId} first, patch only the fields you want to change, and PUT the merged object back. Sending a partial body replaces every other scan setting (scope, authentication, custom headers, …) with defaults.
Validating authentication configuration¶
You can validate an authentication configuration without running a full scan. This is useful in CI/CD pipelines to verify credentials before triggering a scan.
-
Start a check —
POST /v3/authenticationswith either aprofileId(to reuse saved authentication from that profile) or a directauthenticationobject (or both — the object overrides the profile). You can optionally passproxyIdordefaultProxyTypeto control which location runs the check.curl -X POST https://public.escape.tech/v3/authentications \ -H "X-ESCAPE-API-KEY: $API_KEY" \ -H "Content-Type: application/json" \ -d '{"profileId": "<PROFILE_ID>"}'The response contains an
idand initialstatus(STARTING). -
Poll for results —
GET /v3/authentications/{id}returnsstatus,progressRatio, chronologicalevents, and (when status isFINISHED) the structuredauthenticationresults.Poll until
statusisFINISHED,FAILED, orCANCELED.
Commenting on issues¶
Add a comment to an existing issue via the API:
curl -X POST https://public.escape.tech/v3/issues/<ISSUE_ID>/activities \
-H "X-ESCAPE-API-KEY: $API_KEY" \
-H "Content-Type: application/json" \
-d '{"comment": "Verified fix deployed to staging"}'
The comment field accepts up to 512 characters. The response returns the created activity with its id, createdAt, kind, and author.
Exporting reports (Beta)¶
Beta
The export endpoints are in beta and may change.
You can programmatically trigger PDF/report exports using the same blocks available in the product UI.
-
Trigger an export —
POST /v3/jobswith a list of reportblocks(each with akindand optionalparams). You can scope the export withscanId,assetWhere,profileWhere, orissueWherefilters.curl -X POST https://public.escape.tech/v3/jobs \ -H "X-ESCAPE-API-KEY: $API_KEY" \ -H "Content-Type: application/json" \ -d '{"blocks": [{"kind": "ISSUE_LIST"}], "scanId": "<SCAN_ID>"}'The response returns a job
id. -
Poll for completion —
GET /v3/jobs/{jobId}returns the jobstatus, parameters, and once complete,artefactswithsignedUrldownload links for the generated files.