IDE Integration Guide¶
The Escape MCP (Model Context Protocol) server can be integrated into various IDEs, including Visual Studio Code, Cursor, Claude Code, and other MCP-compatible editors. This guide demonstrates configuration for accessing Escape's capabilities directly within your development environment.
Prerequisites¶
- An active Escape account
- Visual Studio Code, Cursor, Claude Code, or another MCP-compatible IDE
- Internet connection to access the Escape MCP server
Step 1: Pick your authentication flow¶
The Escape MCP server supports two flows. Both end up calling the same Public API on your behalf — pick whichever fits your IDE and workflow:
- OAuth 2.1 (recommended) — your IDE opens a browser, you click Allow on a consent page hosted on
app.escape.tech, and the IDE silently receives a bearer token. No API key copy-paste, nothing to commit to git. Works with any client implementing the MCP 2025-06-18 Authorization spec — Cursor, Claude Code, Claude Desktop, ChatGPT desktop, Continue.dev, Zed, Windsurf, Codeium, and any future MCP-compliant client. - Static API key (
Authorization: KeyorX-ESCAPE-API-KEY) — pass your key as an HTTP header in the IDE config. Required for clients that don't yet implement the OAuth handshake, and for headless / CI environments. Works in every MCP client.
If you're not sure which to pick: try OAuth first; fall back to the static key only if your IDE's MCP support doesn't perform the handshake yet.
For the static-key flow, obtain an API key from your User Settings and keep it handy. For the OAuth flow, no API key is needed in the IDE config — but the OAuth consent grants your IDE access to the same User.apiKey under the hood.
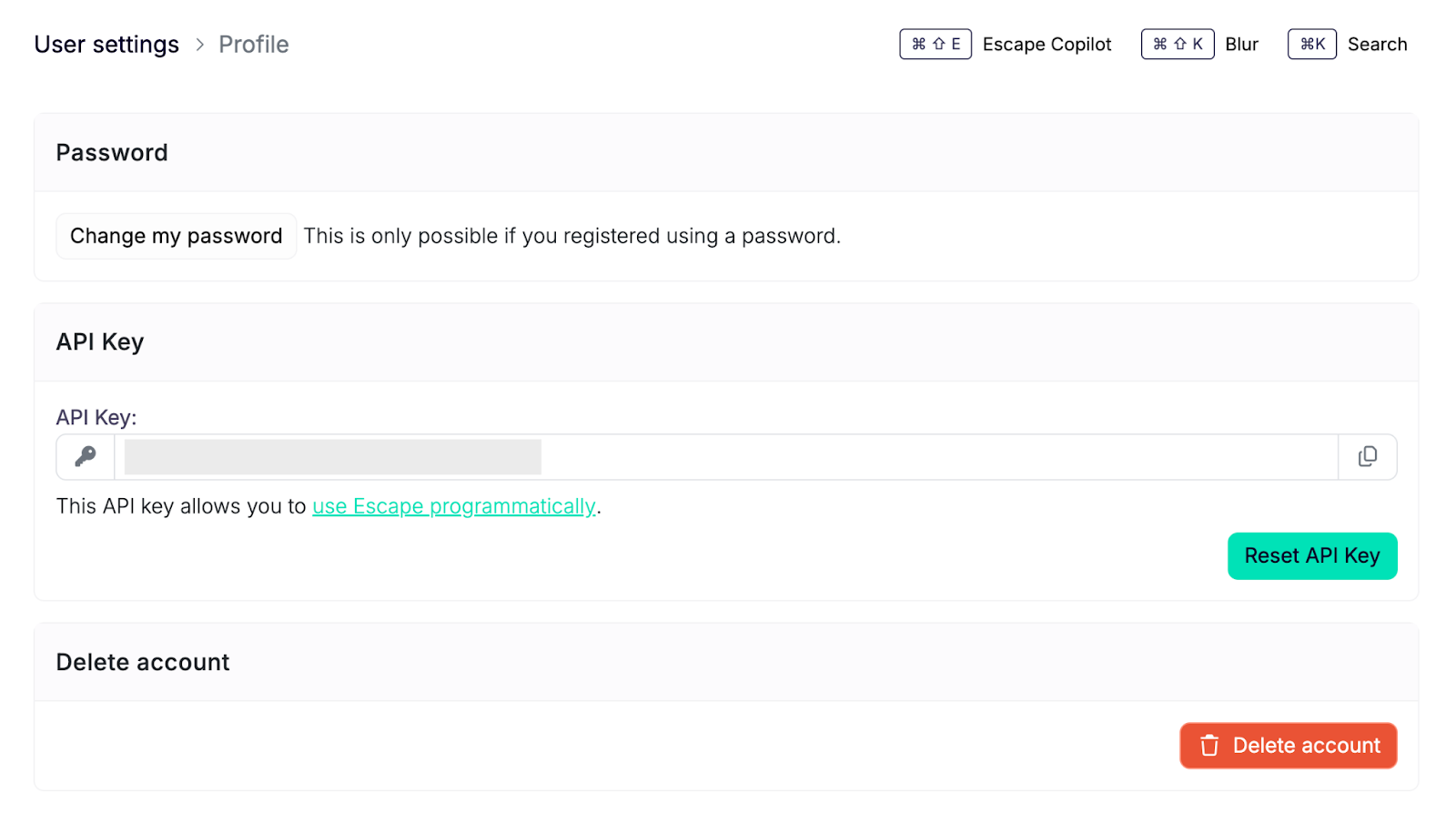
API Key Security (static-key flow only)
API keys provide full access to your Escape account through the Public API. Store your API key securely and never commit it to version control systems. Treat it with the same care as a password. The OAuth flow avoids this risk entirely — the key never leaves the dashboard.
Step 2: Configure MCP Server in Your IDE¶
Visual Studio Code¶
Visual Studio Code provides native support for MCP servers through the MCP extension.
-
Create or edit
.vscode/mcp.jsonin your workspace root. -
Add the Escape MCP server configuration. Pick the tab matching your auth flow:
On the first tool call, VS Code will open your browser to
https://app.escape.tech/oauth/mcp/authorize, you click Allow, and the bearer token is cached locally by the IDE. -
Save the file and reload VS Code.
Workspace vs Global Configuration
The .vscode/mcp.json file is workspace-specific. For global configuration across all projects, consult the VS Code MCP documentation.
Cursor¶
Cursor implements the OAuth 2.1 handshake natively, so the recommended flow is the no-headers one:
-
Open Cursor Settings → MCP (or edit
~/.cursor/mcp.json). -
Add:
-
On first use, Cursor opens a browser to the consent page; click Allow. No API key required.
Use the same mcp.json shape as VS Code above (headers.X-ESCAPE-API-KEY). Useful if you specifically want to scope which Escape user the IDE acts as without going through the dashboard session.
Claude Code (CLI)¶
Claude Code supports both flows. The OAuth one is preferred for interactive use, the header form for headless/scripted contexts.
Add to your Claude Code MCP config (typically ~/.config/claude/mcp.json or via claude mcp add):
On first use, Claude Code opens a browser for the consent page.
Other IDEs and MCP clients¶
Any client implementing the Model Context Protocol can connect to the Escape MCP server. The verified compatible clients with native OAuth support are:
| Client | OAuth callback host (must be allowlisted) |
|---|---|
| Claude Desktop / Web | claude.ai, *.anthropic.com |
| Cowork | cowork.ai, *.cowork.ai |
| Cursor | cursor.com, *.cursor.com, cursor.sh, *.cursor.sh |
| OpenAI ChatGPT / Codex | openai.com, *.openai.com, chatgpt.com, *.chatgpt.com |
| Continue.dev | continue.dev, *.continue.dev |
| Zed | zed.dev, *.zed.dev |
| Windsurf / Codeium | windsurf.com, *.windsurf.com, codeium.com, *.codeium.com |
| Any IDE on localhost | http://127.0.0.1:*, http://localhost:*, http://[::1]:* |
Clients using a custom URI scheme (vscode://, cline://, …) typically fall back to a loopback redirect, which is already accepted.
For clients without OAuth support, the static-key fallback works universally:
- Endpoint:
https://mcp.escape.tech/mcp - Authentication header:
Authorization: Key your_api_key_hereorX-ESCAPE-API-KEY: your_api_key_here - Protocol: HTTP-based MCP
Consult your IDE's documentation for specific MCP server configuration instructions.
Step 3: Verify the Connection¶
After configuration, verification ensures the MCP server is accessible and operational within your IDE.
-
Restart your IDE or reload the window
- VS Code:
Ctrl+Shift+P→ "Developer: Reload Window" - Cursor:
Cmd+R(macOS) orCtrl+R(Windows/Linux) - Claude Code:
claude mcp listto confirmescapeis registered
- VS Code:
-
Open your AI assistant interface (Copilot, Claude, etc.)
-
OAuth flow only — on the very first use, your browser opens at
https://app.escape.tech/oauth/mcp/authorize. Click Allow to grant the IDE access. The token is then cached locally; subsequent sessions skip this step. -
Verify that Escape MCP tools are available in the tool list
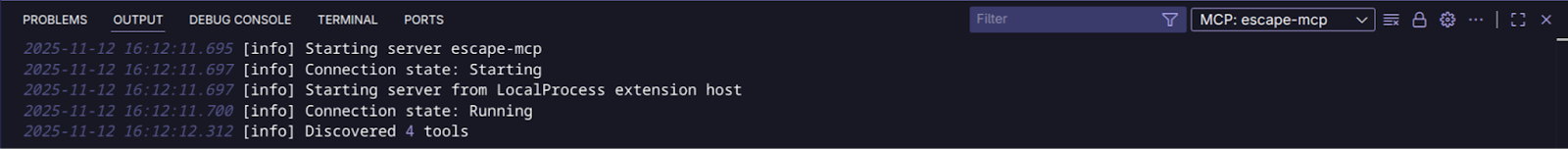
Connection Verified
When properly configured, the Escape MCP server provides access to application management, scan operations, domain management, and security analysis capabilities directly within your IDE.
Vulnerability Remediation in Your IDE
Once configured, you can use the Escape MCP server as a powerful remediation tool directly in your IDE. Learn how to fix vulnerabilities without leaving your development environment in this blog article about fixing vulnerabilities with MCP.
Troubleshooting¶
MCP Server Not Appearing¶
- Verify the
mcp.jsonfile is in the correct location (.vscode/mcp.jsonat workspace root,~/.cursor/mcp.jsonfor Cursor, the path printed byclaude mcp listfor Claude Code). - Confirm JSON syntax is valid (use a JSON validator).
- For the static-key flow, ensure the API key is correct and has not been regenerated.
- Restart the IDE after configuration changes.
OAuth flow: browser doesn't open / consent page rejects the redirect¶
- The MCP server enforces a redirect-URI allowlist — your client's callback host must match. If you're using an unsupported client and seeing
redirect_uri rejected, fall back to the static-key flow or ask Escape support to allowlist the host. - If the consent page reports
redirect_uri rejectedfor a localhost callback, double-check the scheme ishttp://(nothttps://) — only loopback exempts the HTTPS requirement. - After clicking Allow, your IDE should redirect back automatically. If nothing happens, check the IDE's MCP / output panel for the
codequery parameter — your IDE may need aclaude/cursor/etc mcp reauthcommand to retry.
OAuth flow: "Connect" button never appears in the IDE¶
Your IDE has cached an OAuth bearer token from a previous session. Disconnect / remove the MCP entry, then re-add it to force a fresh handshake. As a server-side reset, rotating your API key from the Escape dashboard invalidates every cached token (OAuth and static alike) on the next call.
Authentication Errors (static-key flow)¶
- Verify the API key is active in your Escape user settings.
- Check that the header is one of
Authorization: Key <key>orX-ESCAPE-API-KEY: <key>(header name inX-ESCAPE-API-KEYis case-sensitive in some HTTP clients). - Ensure the API key has not been revoked or regenerated.
Connection Timeouts¶
- Confirm internet connectivity.
- Verify your network allows HTTPS connections to
https://mcp.escape.techand (for OAuth)https://app.escape.tech. - Check for proxy or firewall configurations that may block the connection.
Security Best Practices¶
- Prefer OAuth where supported: removes the API key from your IDE config entirely and avoids any risk of accidental commit.
- Never commit API keys: For the static-key flow, add
.vscode/mcp.json(and equivalents) to your.gitignore. - Use environment variables: Consider referencing environment variables in your MCP configuration if your IDE supports it.
- Rotate keys regularly: Periodically regenerate API keys in your Escape user settings — this also resets cached OAuth tokens.
- Scope access appropriately: API keys (and OAuth tokens, which wrap the same key) inherit your user permissions — ensure your account has only the necessary access level.
Next Steps¶
- Explore Escape Copilot capabilities
- Review the Public API documentation
- Configure automated scanning workflows
Related Documentation¶
- Model Context Protocol Specification
- Escape Public API
- Application Management
- Business Logic Aware DAST Scanning